One aspect of risk is the people in the company. In a sample company one has management, sales, production of a product or service (workers), the workers might have some managers.
The office workers of HR , secretaries of the boss (or president) as well as others like the accounting department. Sometimes a financial officer is needed (not just the book keepers and CPA’s).
Of course besides the office and production people there is the IT department. Why mention all the different types of employees? Who is in charge of cyber attacks?
It would seem that most companies should leave the cyber attacks to the IT department which might consist of a manager for larger organizations as well as the technicians. But remember everyone gets an email so an attack can come from any employee inadvertently (by spam/phishing). Giving some employees high levels of power in installing IT can be dangerous because spam/phishing becomes much more risky since “impact” is increased.
Who is attacking the organization?
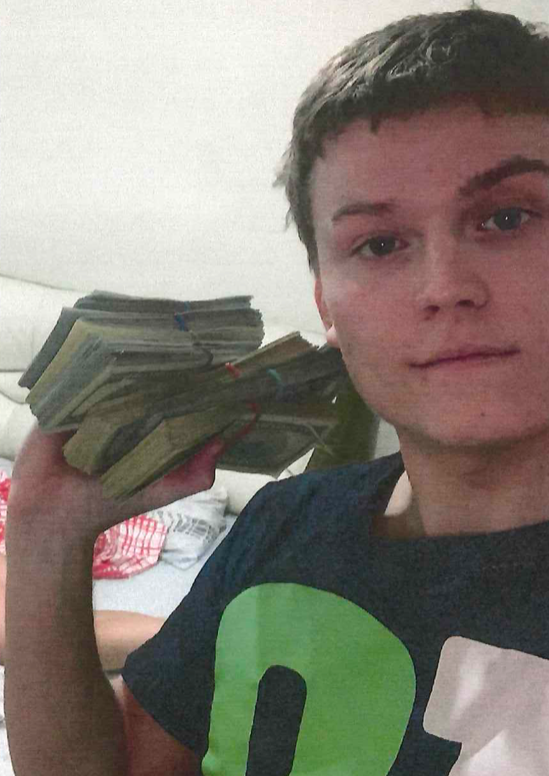
How about this guy: This is the hacker that created “Raccoon” malware which inserts itself into various systems and controls machines until the user pays (also called ransomware). Among the articles about this hacker is an article on Hackernews.com .
It is always a matter of risk isn’t it? How dangerous can a Cyberattack be?
Well the Raccoon malware designer (picture above with a wad of cash in hand) stole 50 million credentials (sets of usernames/passwords). These credentials can be sold in the open market (on the darknet of course).
As business owners one must decide what is a important to spend time and money on? It is very difficult to defend computers when all your credentials are compromised.
This infographic outlines the 4 different types of attackers that need to be kept in mind… categorizing risk and comparing ti to all the different vulnerabilities and possibilities of attack should be used to create a matrix of Risk within your organization.
- Hackers that have money as a goal (steal your money, make money by selling their malware code)
- Nation States (CRINK) China – Russia – Iran – North Korea)
- Anonymous – a nebulous amount of attackers which have an agenda
- Script Kiddies and insiders – maybe not very sophisticated but have drive and are interested in some technical methodology for their aims.
Each attack type has a different impact and likelihood probability which together makes up the risk (RISK= Impact*Likelihood)

Contact me to discuss your risks and how we can reduce risks.
You can also follow me on the various social media to discuss this and other cybersecurity issues.
