Contact me right now at 314-504-3974 Tony Zafiropoulos or email me t o n y z @ f i x v i r u s.com (making it harder for the harvesting email bots out there)
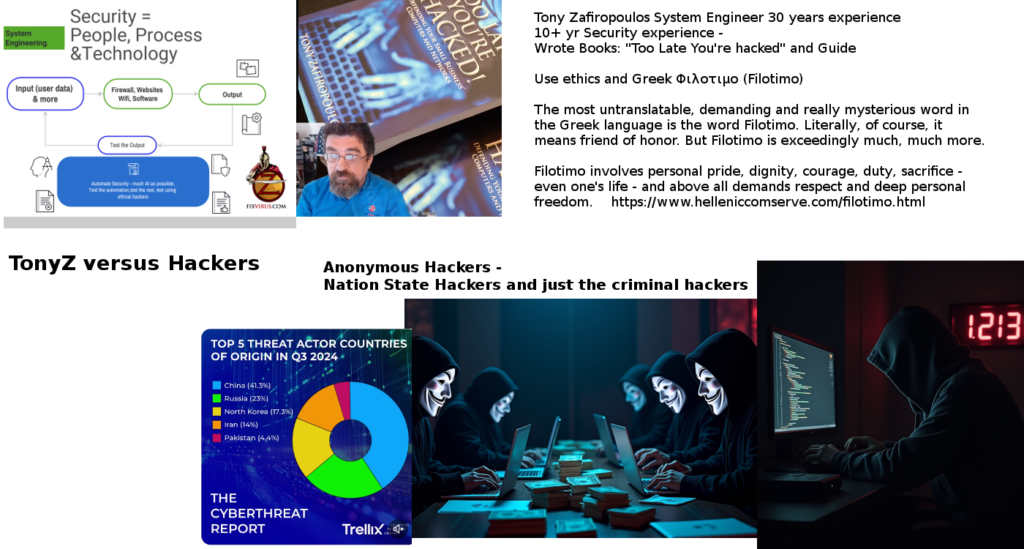
Let me show you who I am with this picture – I also have a video log at https://fixvirus.com/fixvirus-video-show

Pingback: After Action Report on my Hacked WordPress Fixvirus.com | Oversite Sentry
Pingback: Test Your Firewall – Have You Firewalked? | Oversite Sentry
Pingback: Cracking Wifi Passwords Easier Than You Think | Oversite Sentry
Pingback: Website Files Ransomed – Not Just Personal Files | Oversite Sentry
Pingback: HIPAA Compliance Equals Basic Security | Fixvirus.com
Pingback: Another Java Cybersecurity Mess | Oversite Sentry
Pingback: Are You Afraid Of Malware Ads? | Oversite Sentry
Pingback: BaaS – Potential Cloud Insecurity | Oversite Sentry
Pingback: What is the Right Effort to Cybersecurity? | Oversite Sentry
Pingback: 2016 New Year – New Firewall? Which One? | Oversite Sentry
Pingback: 20 Unpatched WordPress Plugins Have Security Flaws | Oversite Sentry
Pingback: ChipAndPin Technology hacked | Oversite Sentry
Pingback: SmartTV Can get malrware & Ransomware | Oversite Sentry
Pingback: SmartTV Can get malware & Ransomware | Oversite Sentry
Pingback: Cloud Not Secure As Rob Alexander(CapitalOne-CIO) Believes | Oversite Sentry
Pingback: Ponmocup: Largest Botnet 500k Infections Currently | Oversite Sentry
Pingback: Ponmocup: Largest Botnet 500k Current Infections | Oversite Sentry
Pingback: TORA! TORA! TORA! Pearl Harbor 74 years ago! | Oversite Sentry
Pingback: Passwords Guessed: Nightmare Scenario | Oversite Sentry
Pingback: How Do You Improve Cybersecurity? Will Not Be Easy! – Oversite Sentry
Pingback: Is Your IT System Low Hanging Fruit For Criminal Hackers? – Oversite Sentry
Pingback: A Single Link Can Destroy Your Data – Oversite Sentry
Pingback: Criminal Hackers Got Your Data in 2015 – Oversite Sentry
Pingback: Happy New Year 2016 – Oversite Sentry
Pingback: SanDisk Wireless Media Drive Hacked in latest issue of 2600 – Oversite Sentry
Pingback: With This Hack Take Over Verizon Email Accounts – Oversite Sentry
Pingback: With Next Gen Firewall: Security Issue Solved? – Oversite Sentry
Pingback: 2016 Cisco Annual Security Report Insight – Oversite Sentry
Pingback: Not Patching in Time Can Hurt – Oversite Sentry
Pingback: Start With Some Cybersecurity – Fixvirus.com
Pingback: What Happens When Everything Done for Cybersecurity Is Not Enough? – Fixvirus.com
Pingback: How Do Hackers Do What They Do? – Oversite Sentry
Pingback: “New” PCI Compliance v3.2 now published – Oversite Sentry
Pingback: Can Logs be Changed By Hackers? – Oversite Sentry
Pingback: Ur Bases Belong To Us – Fixvirus.com
Pingback: Want Internet? Then Cybersecurity is a Must – Fixvirus.com
Pingback: Criminals Value Your Computer Infrastructure & Can Make 5000% Return With Ransomware – Fixvirus.com
Pingback: What is Your Hacked Computer Worth? – Fixvirus.com
Pingback: Why Should a Business Use An Outside Consultant-Reviewer? – Fixvirus.com
Pingback: April-May Spring Cleaning – Fixvirus.com
Pingback: 3rd Quarter 2018 has started – Fixvirus.com
Pingback: Cyberthreats Increasing Using Easy to Use Tools for Hackers – Fixvirus.com
Pingback: Innovation and Cybersecurity – Explaining Security
Pingback: Computer Security in 2019 – Fixvirus.com
Pingback: Compliance vs Framework – Explaining Security
Pingback: PCI Compliance can be a good Start to a Security Policy – Fixvirus.com
Pingback: Our Cybersecurity Catch22 – Fixvirus.com
Pingback: APC UPS (Power Supplies) 3 Critical Vulnerabilities – A Fixvirus Blog
Pingback: Twitter Site Claims to Know Ransomware Targets – A Fixvirus Blog
Pingback: AI Can Be Dangerous For Cyberdefense or Privacy – A Fixvirus Blog
Pingback: Risk Management AI Framework by NIST – Oversitesentry -A Fixvirus Blog
Pingback: HIPAA Rules Upgrade What it Means? – Oversitesentry -A Fixvirus Blog
Pingback: Kostas Talks Cybersecurity – Oversitesentry -A Fixvirus Blog