People keep asking me… what can someone possibly use on my computer, I have nothing on it.
We are trying to explain this with some images
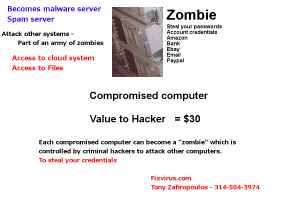
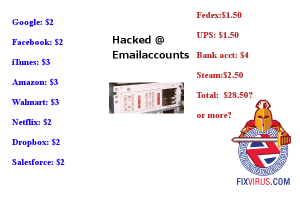
The hacked computer could have a value of about $30
Zombie computer: being controlled by other computers
A hacked computer (now is called a Zombie) when it is used as an attack vehicle.
This system can be on the corporate network, could be a phone, or an “Internet of things”
Any device on the Internet has the potential to become a Zombie, and to be used as an attack vehicle.
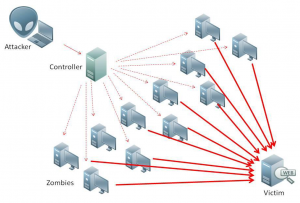
When controlled from a single machine to reflectors one can control hundreds even thousands of computers.
Here is an analysis of using reflectors in DDOS http://www.icir.org/vern/papers/reflectors.CCR.01/reflectors.html
(Image from Datasoft: https://www.datasoft.ws/ds_whatisddos.php)
The above image is a good representation of what a DDOS reflector attack consists of.
So yes your hacked machine is worth $30 or more even if you do not have “valuable” data on it. the problem is, any password that you saved on the system could be used by the hacker to penetrate your life identity on the Internet
And of course in 6/27/16 I put up a new blogpost at my site http://oversitesentry.com/iot-botnet-can-ddos-your-webserver/
Briefly it is about a 25000 CCTV botnet which were all hackedand now are used to attack other machines.
Contact me to discuss how we can design a vulnerability analysis on your computer network.