Cybersecurity for Small Business in 2026
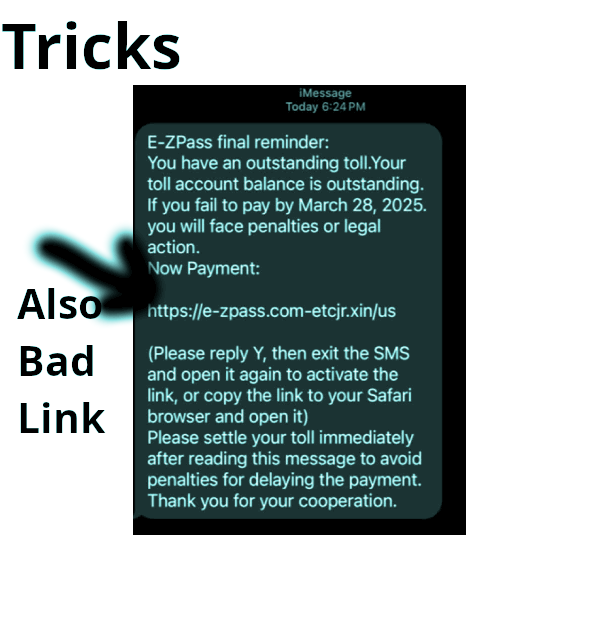
What has to happen to have a successful cybersecurity program? It does not have to cost a lot… Lets set this with numbers 1-4 EDR, Firewall, Security policy-training, update systems. 1. Protect Your Devices: Antivirus… Cybersecurity for Small Business in 2026