As Robert Graham says in his blog Errata¹ It is Human nature to do a number of Cybersecurity No No including fall for Phishing scams (even the experts fall for them). A well crafted email will look like it is coming from a trusted source not from a stranger. So to avoid phishing scams one needs to look for more than just “is this email from someone I know?”
- A phishing Scam is where an unsuspecting email user clicks on a fake email and on it’s attachment. The attachment then infects the computer due to the malicious software(malware) actually hiding within the attachment.
- Password reuse – due to laziness and bad practices employees use the same passwords on several sites. When a weak security site is hacked the hacker has your password and now can guess where else you might use it (banks, email account, and more)
- SQL injection (for programmers). This is a computer programmer topic.
Consistently reusing passwords across many sites is human nature (laziness). But doing so in your hobby site and using the same password in your email account and facebook is a recipe for disaster.
Once a hacker has your email account they can change everything.
For the programmer it requires more work to sanitize data input and to make sure that an attacker won’t use an ingenious method to insert some malicious code
Is Robert right? Are people really ‘stupid’ regarding these 3 items?
I would not be so harsh as to call everyone Stupid.
As a society we will be hacked in one form or another, but the reason is not stupidity, as most people understand the basics that hacking means to use ingenious ways to get around the standard.
Another thought that is wrong in general is the false belief that we could design something that is foolproof, or at least it does not have to be worked on constantly.
I think we need to assume that we will need to consistently patch and fix our computers. we also need to see that the computer is a tool written by humans and used by humans.
Unless one has the mindset of the attacker and the tools and setup of sophisticated attacks one cannot really see the potential dangers under every rock. The IT people in every company are busy trying to connect and work on every system in your network. They do not spend every day researching new attack methods. Attacking test computers
You have to have a separate group of people with a separate pair of eyes to review your network defense, computer system setup and more.
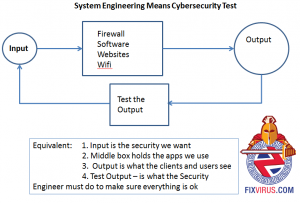
Let me explain it for you if you still have questions.
Tony Zafiropoulos – 314-504-3974
- http://blog.erratasec.com/